Seamlessly Secure eSignatures with Box Sign – An Overview
What is Box Sign? Box Sign is a comprehensive eSignature solution seamlessly integrated into the Box content cloud ecosystem. This platform facilitates a secure and efficient signing process for documents online. Made accessible to our community at https://olemiss.app.box.com, faculty and staff can effortlessly upload documents, establish customizable templates for recurrent use, and dispatch these documents […]
Office Activation Instructions
The University of Mississippi now provides Microsoft Office 365 for all faculty, staff and students at no charge. PLEASE NOTE: Office 365 is a subscription-based license. If you have an existing perpetual license for Microsoft Office on your computer, it may make sense for you to stop here and continue using that license. This is […]
Introducing eSignature Solutions with HelloSign – Updated
What is HelloSign? HelloSign is an eSignature technology that allows people to sign documents virtually. Available at olemiss.edu/hellosign, teams and departments at the University will be able to upload documents, create templates that can be shared and reused amongst team members, then send those documents to users who can sign and return their legally binding […]
Calendly
Calendly is a service that makes your Outlook Calendar’s free time visible for people trying to schedule appointments with you.
Zoom Chat for Real-Time Collaboration
With UM organizations of all kinds working to advance their missions while maintaining all required social distancing protocols, IT has received a number of inquiries about implementing a university-wide instant messaging solution. Fortunately, such a product is already available to all UM employees and students. The Chat feature built into Zoom has all of the […]
Security Changes to Zoom Effective 9/27/20
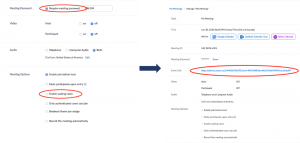
As part of ongoing efforts to fight “Zoom-bombing” and promote safe and secure online meeting spaces, on 27 September 2020 Zoom will require that all meetings have a Passcode or a Waiting Room enabled for all accounts. Zoom users are in control of meeting security selections, and Zoom has designed the options with security and […]
Update Your Student Contact Info
Update your contact information now!