Phishing emails look authentic. They often have links to exact replicas of our portals, spoofed sender addresses, and malicious attachments with convincing file names.
How Do I Identify Phishing?
Closely examining website addresses, email links, and sender addresses can help you determine if an email is legitimate or not. One simple way to do this is by using the hover technique. This is done by resting your pointer over the link in an email (or by long-pressing it on a mobile device). In most cases this will reveal the true address, without clicking the link.
From here you can determine if the addresses are recognizable and trusted. For example, an official email from olemiss.edu would normally not have a link that goes to xyz.com. Similarly, an email from UM would normally not come from an outside address such as user@yahoo.com.
It is important to note that the sign-in page to student email is ONLY valid if the website address is something.google.com. Also note that UM does use external email services for particular needs; however these non-olemiss.edu emails and linked websites should NEVER ask for sensitive information like your UM password directly. Lastly, the validity of any UM Today (daily or express) email can be verified by checking the announcements section in myOleMiss.
In summary, always pay close attention to the website address. Phishing can come through email, social medial, text messaging, online advertising, gaming, and instructions given over the phone. If you land on an address that is NOT in the format https://something.olemiss.edu, and it asks for your UM password, it is likely phishing.
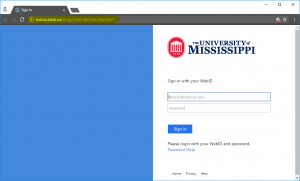
What’s wrong with this picture? The website is not an ‘olemiss.edu’ address. Phishing portal – Stop!
How Do I Report Phishing?
If you receive a phishing email related to UM, forward the message to abuse@olemiss.edu. If the email appears to come from another known organization, consider contacting that organization directly. Always mark the message as spam/junk/phishing in your email client.
If you think you may have released personal information by way of a phishing scam, report the incident to the involved organization directly using the contact information on their website. You should also immediately change your password to their service. Then monitor your account for other suspicious activity.
For more information, contact the IT Helpdesk or visit the IT Security website.
Tags: Email, infosec, IT Security, Phishing, Scam